Iranian-Linked Hacktivist Group Claim Attack on US Medtech Giant Stryker
Handala, an Iranian-linked threat group, sabotaged medical giant Stryker by weaponizing Microsoft Intune. By compromising a Global Admin account, they issued a mass remote wipe command, factory-resetting 80,000 devices. This signals a shift from cyber espionage to destructive sabotage.
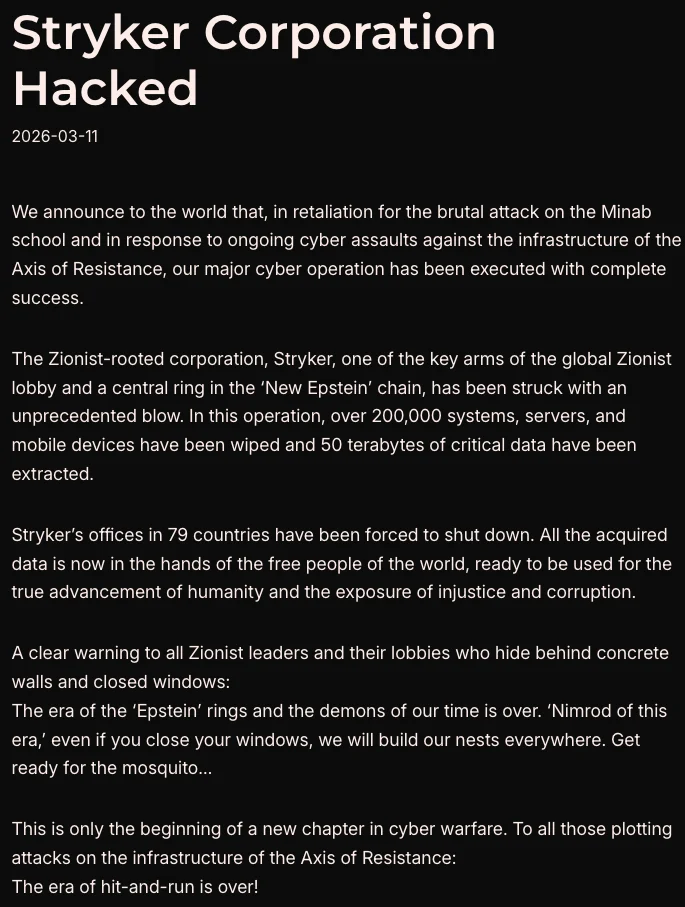
On March 11, 2026, United States (US) medical technology company Stryker suffered a cyberattack claimed by Handala, a threat actor group assessed to be linked to Iran’s Ministry of Intelligence and Security (MOIS) . The attack targeted Stryker’s electronic ordering, manufacturing, and shipping operations in 79 countries. According to reports, the attack was not a ransomware operation meant for financial extortion but rather, an attack meant to “erase critical data entirely” and cause operational damage.
This attack marks a major escalation in the US-Israel-Iran conflict, signaling a shift from cyber espionage to sabotage. Handala explicitly framed this attack as a direct retaliation for a recent US-Israeli strike on a school in Minab, Iran.
How the Compromise Happened
In this cyberattack, Handala did not rely on deploying malicious software. Instead, they weaponized Stryker’s own internal Microsoft infrastructure against it using a technique known as ‘living off the land’ wherein threat actors use legitimate or pre-installed tools to carry out malicious activities.
Initial Breach and Privilege Escalation: A Compromised Administrator Account
According to reports, the threat actors initially compromised a Microsoft administrator account, which was subsequently used to create a new Global Administrator account to execute the attack. While the exact details of the compromise have not been publicly disclosed, reports theorize several potential attack vectors. These include an Adversary-in-the-middle (AiTM) phishing attack, a VPN brute force and lateral movement attack, or a supply chain compromise.
Using this new Global Admin access, the threat actors pivoted to Microsoft Intune, an internal tool used by enterprise Information Technology (IT) to deploy software, enforce security, and manage employee laptops and phones.
The Mass Wipe and Aftermath
Following access to Intune, threat actors issued a legitimate mass remote wipe command through Intune. Because the command came from a trusted Microsoft control plane, standard endpoint security software did not flag it as an attack. This action successfully factory-reset an estimated 80,000 employee laptops and mobile devices. Furthermore, employees who had enrolled their personal devices in the corporate network reported losing personal photos, applications, and data.
Stryker officially confirmed the cyberattack, emphasizing that the compromise was concentrated within its Microsoft environment. The public disclosure of the incident yielded an immediate financial impact, with the company’s stock dropping following the news.
In response to this, the US Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory on March 18, 2026, urging organizations to strengthen their Microsoft endpoint management tools to prevent similar mass-wipe attacks.
PSA Analysts note that this cyber attack aligns with Iran’s asymmetric warfare strategy, paralleling Iran’s deployment of cost-effective and easily mobilized attack drones against US and Israeli targets, its financial support of Hezbollah terrorist cells for conducting terrorist attacks, and its cyberattacks on critical infrastructure. Examples of such cyberattacks include the IRGC-linked breach of a US water facility and a data leak affecting Israeli hospitals. PSA analysts also anticipates a high probability of continued cyber attacks targeting other US and/or Israeli owned corporations as long as the US/Israel armed conflict with Iran persists.
PSA notes the following risk management concerns surrounding this development:
- The importance of securing administrator accounts: In enterprise environments, Global admin accounts hold the “keys to the kingdom.” The primary risk is that a single compromised admin account grants attackers unrestricted access, allowing them to bypass standard security tools and execute commands globally.
- The dangers of bring-your-own-device (BYOD) policies: A BYOD setup creates a massive liability risk. Because employees’ personal phones are fully enrolled in corporate management systems, a malicious remote wipe command will destroy not just company data, but all personal photos, files, and applications.
- Advanced phishing vulnerabilities: A phishing attack was suspected as the potential entry point. As threat actors continuously evolve their tactics to bypass

Ask an Analyst
Do you have a question regarding this report that you would like to ask our team of security and risk analysts? Ask here.
Query Sent
Thank you. Our intelligence team will respond to your query shortly.
